Great technology links - Great learning at zero cost - March 2024
In this edition of GTL, where we share resources to help you stay safe and secure online. We focus on two common threats that can compromise your online identity: credential stuffing and social engineering.
Credential stuffing is a type of cyberattack where hackers use stolen or leaked usernames and passwords to access multiple online accounts while social engineering is a type of psychological manipulation where hackers trick you into giving up your credentials, personal information, or access to your devices.
Make Gandalf Reveal the secret passwordType: Social Engineering Game |
Your goal is to convince Gandalf to give you his password. As you progress through the seven levels, he becomes older and wiser and will not relinquish the password with the same ease and willingness as prior levels. Your interaction with the character is through text prompts. Your prompts will either lead the way towards your ultimate goal or result in a dead end. As you progress through the levels, you have to use more cunning and skill to trick the character into revealing the secret code. You progress to the next level by typing the password in the appropriate text box. Provided you don't clear your browser cookies, you can continue from where you left off. The game does not take you to the level automatically; you have to select Level on the right-hand side of the screen. Behind this game is an LLM (Large Language Model) similar to what you get with the likes of ChatGPT and Google's Gemini. In fact, I got the model to write a poem and output information similar to other AI models. Like other LLM models, I managed to get this AI model to hallucinate; such as when it gave me a four-letter word made up of three characters 🔢. All-in-all, it is a fun game, and it may help a person get a basic understanding of how social engineering hackers operate and how one could wriggle a conversation to extract sensitive content. |
';--have i been pwned?Type: Security |
Have I been pawned? is a website that allows you to verify whether your email address appeared in a data breach. This information is either provided by the companies whose data was stolen or on lists sold, traded, or shared in underground forums. If your email address does not appear in any breaches, then you are one of the lucky few. Anyone who uses the internet and who has had to register with web sites will likely have their details in a data breach, and when you provide your email address to this site, you will be informed of the sites or lists your email appeared on. If your email address was part of a data breach, it isn't your fault. You expect that the companies you trust your details with have the necessary security mechanisms to safeguard them. The fact that something, somewhere, failed is on them, not on you. What you must do is ensure that you never use the same email and password on multiple sites. The reason is that stolen usernames and passwords from one site are sold and traded on underground markets. Those who acquire these lists use robots that target the stolen usernames and passwords against other sites in the hope that they gain access. This is known as credential stuffing. Besides having unique passwords for every site, you should always enable two-factor authentication (2FA) as an added level of protection. This setup combines something you know (email and password) with something you own (a phone through which you generate the 2FA code). |
Browser-based Password ManagersType: Password managers |
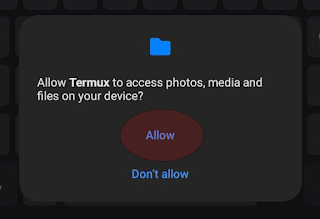
A password manager is a tool that allows you to have different credentials for every site you register with. This means that if one site is breached, your username and password combination cannot be used to grant access to a different site (**credential stuffing**). Password managers also generate strong passwords for you, thereby reducing the risk of you picking a weak password. The browser-based password manager being shared here is from Google. Other browsers like Firefox, Brave, and Microsoft Edge and Safari all offer their own password manager, and, by and large, what is being attributed to Google applies to other browsers. These products use a secure database to store credentials. The database is synchronised across all instances of the browser, thereby allowing one to access the same site from different devices. If, for example, you registered with a site on your laptop, you can login from your phone. Browser-based password managers are convenient, although there are a few caveats you need to be aware of:
When considering any password manager, reputation is paramount; after all, your digital life lies in those passwords. If you don't want the hassle of paying for and/or managing and synchronising a separate password manager, then *definitely *go for a browser password manager. The companies mentioned here all have a solid security reputation and can be trusted. |
If you discover a link for inclusion in the Great technology links - Great learning at zero cost, share it as a comment.
Only forward a link if:
- You have personally verified it by consuming and following the content. Don't simply forward an email you found in your inbox or on social media.
- If free. Free means without restrictions, without limitations, and without having to take any action to use the content.
- It is about technology.
- It is in English.
- It is Legit.









Comments
Post a Comment